เริ่มต้นใช้งาน
ข้อมูลหลัก
อื่นๆ
ยืนยันด้วย SEEK Pass
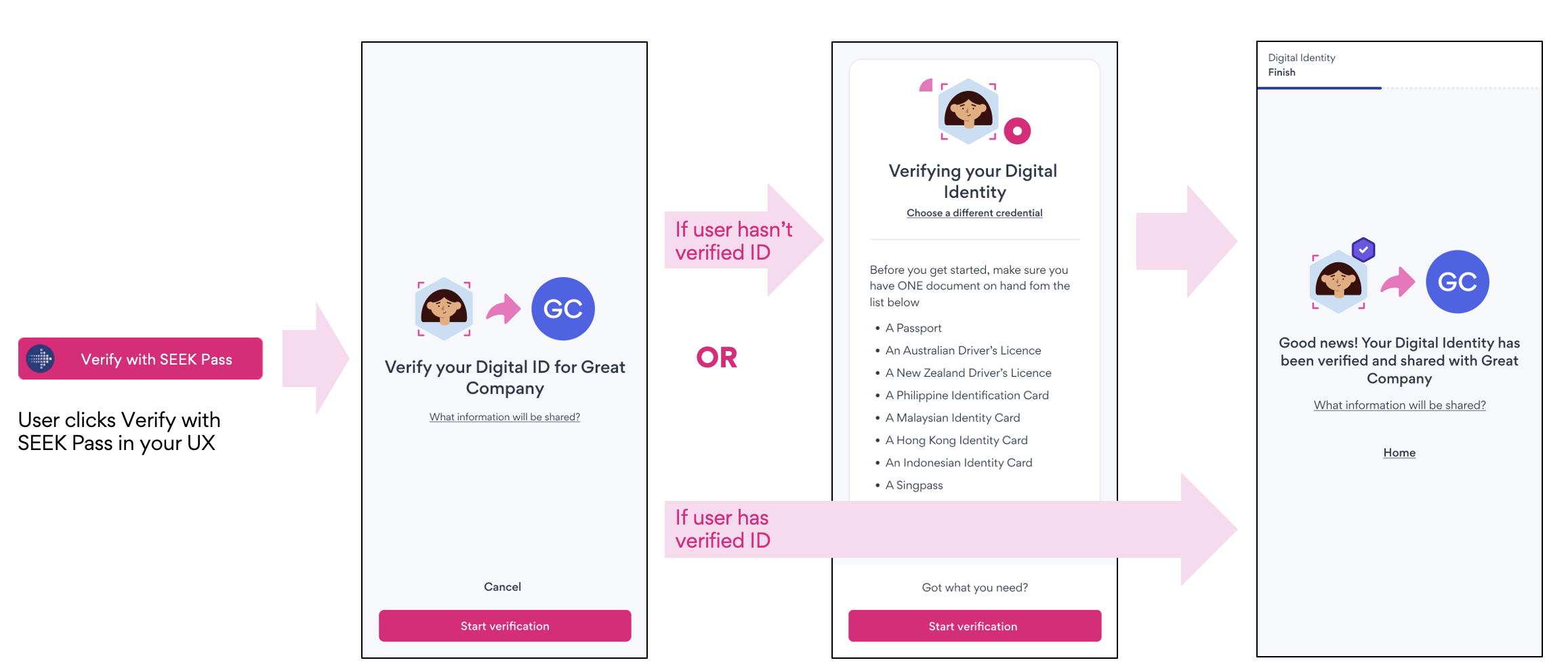
ยืนยันด้วย SEEK Pass มอบวิธีที่ราบรื่นสำหรับการยืนยันข้อมูลรับรอง (เช่น ตัวตนดิจิทัล) ผ่าน SEEK Pass สำหรับการผสานรวมนี้ พันธมิตรจะฝังปุ่มไว้ในขั้นตอนการใช้งานของตน ซึ่งจะนำผู้ใช้ไปยังแอป SEEK Pass ที่ผู้ใช้ต้องเลือกข้อมูลรับรองที่จะยืนยัน (เช่น หนังสือเดินทาง ใบขับขี่) พันธมิตรสามารถผสานรวมกับ SEEK Pass โดยใช้ REST APIs เพื่อตรวจสอบสิทธิ์และสร้างคำขอการยืนยัน และเปลี่ยนเส้นทางผู้ใช้ไปยังแอป SEEK Pass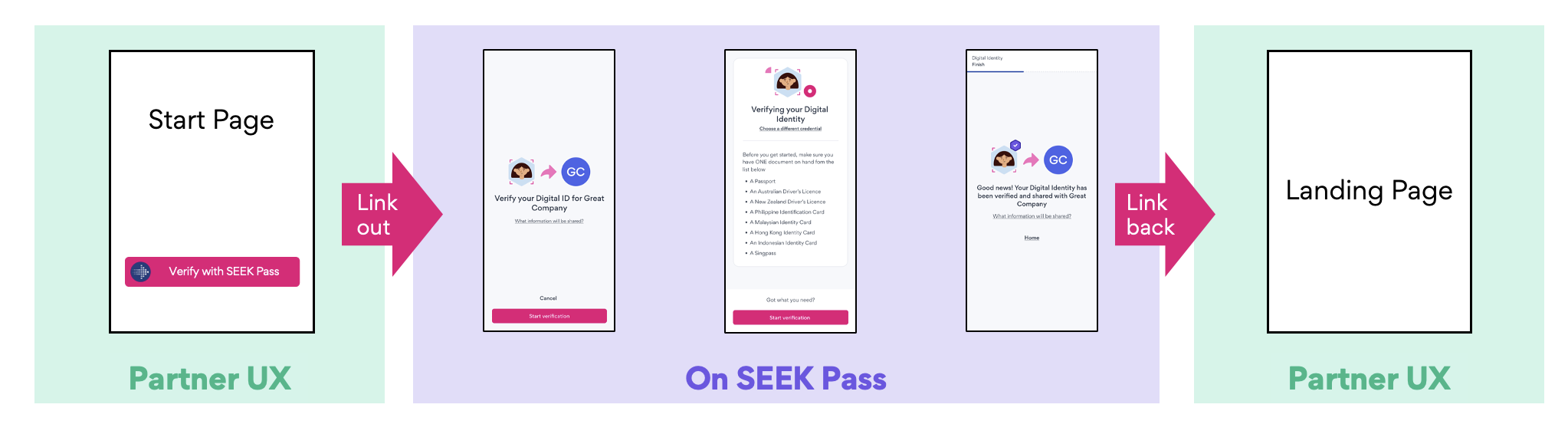
รายละเอียดทางเทคนิค
การเชื่อมต่อนี้มี 3 ระยะ:- การยืนยันตัวตนกับ SEEK Pass
- การส่งคำขอการยืนยัน
- กำลังดึงผลการยืนยัน
# POST /api/partner/v1/oauth/token
curl --location $SEEK_PASS_URL/api/partner/v1/oauth/token.json
--header 'Accept: application/json'
--header 'Content-Type: application/x-www-form-urlencoded'
--data-urlencode grant_type=client_credentials
--data-urlencode client_id=$CLIENT_ID
--data-urlencode client_secret=$CLIENT_SECRET
--data-urlencode 'scope=write.digital_identity read.digital_identity'เพย์โหลดคำขอ
เพย์โหลดคำขอมีฟิลด์ดังนี้:- request_id (ไม่บังคับ): ใช้ให้พาร์ทเนอร์ติดตามคำขอของตน หากไม่ระบุ ระบบจะสร้างให้อัตโนมัติ
- callback_url (ไม่บังคับ): หากระบุ ผู้ใช้จะถูกส่งกลับไปยัง URL นี้หลังทำขั้นตอนการยืนยันตัวตนให้เสร็จสิ้น
- display_options (required): ค่า partner_name ที่จำเป็นต้องระบุจะแสดงให้ผู้ใช้เห็น สามารถระบุ partner_logo_url เพิ่มเติมได้
- request_source (ไม่บังคับ): ฟิลด์นี้บันทึกลำดับชั้นของฝ่ายที่เกี่ยวข้องในคำขอการยืนยันตัวตน (เช่น ATS)
- metadata (ไม่บังคับ): ฟิลด์นี้เก็บข้อมูลเพิ่มเติมที่ SEEK Pass ต้องการเพื่อการรายงานหรือวัตถุประสงค์อื่น สำหรับ SEEK/Indirect เราจะบันทึกข้อมูลที่เกี่ยวข้องกับงาน
หากไม่มี request_id ในเพย์โหลดคำขอ SEEK Pass จะสร้าง request ID ที่ไม่ซ้ำให้อัตโนมัติ เราแนะนำให้ใช้ค่าที่ไม่ซ้ำทั่วโลก (เช่น UUID) สำหรับ request_id เพื่อให้ติดตามคำขอของผู้ใช้ได้อย่างถูกต้อง
# POST /api/partner/v2/verify/requests/digital_identity.json
{
"request_id": "7cbc7e51-82f5-43ec-8d63-b7cdf1170425", // Optional. For tracking requests. If not passed, it will be auto-generated.
"callback_url": "https://www.partner.com/callback", // Optional. For redirecting users
"display_options": { // Required
"partner_name": "string", // Required
"partner_logo_url": "string" // Optional
},
"request_source": [ // Optional
{
"name": "string"
}
],
"metadata": { // Optional - context about the verification
"position_title": "string",
"position_url": "string",
"position_location": "string",
"job_categories": "string",
"applied_on_seek": true
}
}{
"request_id": "7cbc7e51-82f5-43ec-8d63-b7cdf1170425",
"redirect_uri": "https://app.seekpass.co/partner/verify/digitalIdentity?clientId=[CLIENT_ID]&requestId=fa651300-b91a-49cb-8ee7-cac68b3fdf74"
}พฤติกรรม
- การใช้ ID ซ้ำภายใน 48 ชั่วโมง: การส่งคำขอด้วย ID ที่มีอยู่ภายใน 48 ชั่วโมงจะส่งคืน
redirect_uriเดิม - การนำ ID มาใช้ซ้ำหลัง 48 ชั่วโมง: หลัง 48 ชั่วโมง ข้อมูลต้นฉบับจะถูกลบอย่างถาวร การส่งใหม่ด้วย ID เดิมจะสร้างคำขอข้อมูลรับรองใหม่ที่มี SEEK Pass ID แยกต่างหาก และสร้าง
redirect_uriใหม่ - การเชื่อมโยงผู้ใช้: เมื่อผู้ใช้เข้าถึง
redirect_uriและยืนยันตัวตน ข้อมูลเอกสารรับรองจะถูกแนบกับบัญชีของผู้ใช้ - Consent Flow: ข้อมูลเอกสารรับรองจะถูกแนบกับบัญชีของผู้ใช้เมื่อยืนยันตัวตน ไม่ว่าสถานะความยินยอมจะเป็นอย่างไร หากยังไม่ได้ให้ความยินยอม
redirect_uriจะแจ้งให้ผู้ใช้ยอมรับ - พฤติกรรมหลังให้ความยินยอม: เมื่อให้ความยินยอมแล้ว คำขอ API ครั้งถัดไปจะส่งคืน URL เดิม โดยนำผู้ใช้ไปยังเอกสารรับรองที่ส่งไว้
- นโยบายการเก็บรักษาข้อมูล: หากผู้ใช้ดำเนินการตามขั้นตอนผู้ใช้เสร็จสิ้น แต่ไม่ได้ดาวน์โหลดและยืนยันตัวตนผ่านแอปมือถือภายใน 48 ชั่วโมง เอกสารทั้งหมดที่เกี่ยวข้องจะถูกลบอย่างปลอดภัยตามนโยบายการคุ้มครองข้อมูล
เมื่อผู้ใช้คลิกลิงก์และเข้าสู่ระบบแล้ว ข้อมูลจะถูกเชื่อมโยงเฉพาะกับผู้ใช้นั้นเท่านั้น หากผู้ใช้อื่นพยายามใช้ลิงก์เดียวกัน ระบบจะนำไปยังหน้าแสดงข้อผิดพลาด
แผนภาพลำดับ

บัญชี SEEK Pass
SEEK Pass จะให้ข้อมูลรับรอง OAuth สำหรับพาร์ทเนอร์เพื่อใช้ยืนยันตัวตนในสภาพแวดล้อม staging และ production ดังนี้:- ปลายทาง OAuth token: POST /api/partner/v2/oauth/token.json
- โฮสต์:
- Production: https://app.seekpass.co
- Staging: https://app.seekpass-staging.com
- ข้อมูลรับรองของไคลเอนต์จะถูกส่งให้ผ่านช่องทางที่ปลอดภัย (เช่น 1Password)
ปุ่ม ยืนยันด้วย SEEK Pass
SEEK Pass มีชุดรูปภาพปุ่มให้พาร์ทเนอร์ของเรา ซึ่งสามารถฝังเพื่อแสดงบนแพลตฟอร์มของคุณได้ รูปภาพเหล่านี้จะแสดงด้วยแบรนด์ SEEK Pass เพื่อให้เกิดความสอดคล้องกันในทุกการโต้ตอบของผู้ใช้ เราแนะนำให้ใช้แอสเซ็ตปุ่มที่จัดเตรียมไว้ให้ทุกครั้งที่เป็นไปได้ เพื่อคงสไตล์ที่สอดคล้องกับแบรนด์ ตัวอย่างปุ่มแสดงอยู่ด้านล่าง สำหรับรายละเอียดเพิ่มเติม โปรดดู เอกสาร API - แนวทางการใช้แบรนด์โครงสร้าง Redirect URI
- พาธ: /partner/verify/[Credential type]
- โฮสต์:
- Production: https://app.seekpass.co
- Staging: https://app.seekpass-staging.com
- คิวรี: พารามิเตอร์ด้านล่างเป็นพารามิเตอร์คิวรีของ URL
- clientId: ID แอปพลิเคชัน OAuth
- requestId: ID คำขอการยืนยัน
- ตัวอย่าง: https://app.seekpass-staging.com/partner/verify/digitalIdentity?clientId=[CLIENT_ID]&requestId=fa651300-b91a-49cb-8ee7-cac68b3fdf74
ผลการยืนยัน
ข้อมูลการยืนยันและผลลัพธ์ของคำขอจะถูกส่งผ่าน API หรือ webhook ที่พาร์ทเนอร์ลงทะเบียนไว้ SEEK Pass สามารถส่งอัปเดต webhook สำหรับเหตุการณ์ต่าง ๆ ในแต่ละขั้นของเวิร์กโฟลว์การยืนยันได้ ตัวอย่างเหตุการณ์แสดงอยู่ด้านล่าง:- incomplete
- canceled (rejected, canceled, expired)
- verified